Sideloading apps isn’t dead – Google just made it more complicated
The landscape of Android app installation is undergoing a significant shift, with Google implementing new developer verification rules that have raised concerns about the future of sideloading. While initial interpretations suggested a potential crackdown on installing applications from outside the official Google Play Store, the company has clarified its stance, confirming that sideloading will remain possible, albeit through a more involved process. This change, dubbed "advanced flow," aims to enhance security and reduce the prevalence of malicious applications while preserving the inherent openness of the Android ecosystem for power users and developers.
Understanding the "Advanced Flow" for Sideloading
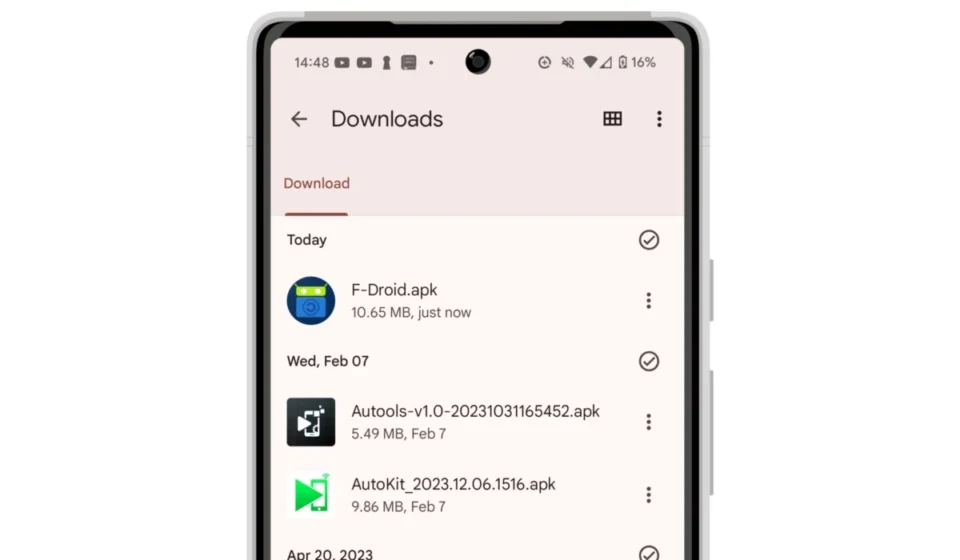
At the heart of this revised approach is Google’s introduction of an "advanced flow" for installing applications that are not sourced from the Google Play Store. Previously, users could enable the "install from unknown sources" setting, granting broad permission to install APK files from various origins. The new system, however, mandates a multi-step verification process, transforming sideloading from a simple toggle to a more deliberate action. This intentionality is a key component of Google’s strategy to deter casual users from inadvertently installing harmful software.

The advanced flow process, as outlined by Google, is designed to be a one-time procedure for users who choose to venture beyond the Play Store. This means that after the initial setup, the process for subsequent sideloaded apps might be streamlined, but the initial barrier is designed to be more robust. While the exact technical specifications of the multi-step verification are still being detailed, it is understood to involve a more rigorous confirmation from the user before an APK file can be executed. This aims to ensure that users are fully aware of the risks involved and are making a conscious decision to proceed with the installation of an application from an unverified source. The emphasis is on informed consent and a higher threshold for user interaction, making it more difficult for malware to be installed through deceptive means.
The Driving Force Behind the Changes: Enhanced Security and Developer Accountability
The implementation of these new sideloading protocols is not an isolated event but rather a component of a broader, ongoing initiative by Google to bolster the security of the Android platform. The company has been progressively tightening its developer verification processes and app review policies to combat the persistent threat of malicious applications. A significant milestone in this effort is the planned enforcement of Android’s requirement for apps to come from verified developers, set to take effect in September 2026. While this mandate will initially target select regions, a wider rollout is anticipated, signaling a fundamental shift in how applications are distributed and managed on the Android operating system.
Google’s primary objective with these stricter measures is to make it significantly harder for malicious actors to distribute harmful applications. Historically, bad actors have exploited loopholes by repeatedly submitting malware under new developer identities after their previous applications were removed from app stores. By requiring verified developer credentials and implementing more stringent checks, Google aims to create a more accountable ecosystem. This not only protects users from malware, phishing attempts, and privacy breaches but also fosters a more trustworthy environment for legitimate developers.

However, Google acknowledges that sideloading is an integral part of the Android experience, contributing to its reputation as an "open" platform. Many developers, particularly those working on niche or experimental applications, rely on the ability to distribute their software directly to users. Furthermore, power users often appreciate the flexibility and control that sideloading offers. Recognizing this, Google has opted for a path that enhances security without entirely eliminating this functionality. The introduction of the advanced flow is a compromise, aiming to strike a balance between robust security and user freedom.
Chronology of Evolving Sideloading Policies
The journey towards the current "advanced flow" has been a gradual evolution. For years, Android users could easily sideload apps by enabling the "Unknown Sources" option in their device settings. This feature, while convenient, also presented a significant security risk if users were not diligent about the origins of the APK files they downloaded.
As the Android ecosystem grew and the sophistication of mobile malware increased, Google began to implement more granular controls. In later Android versions, the permission to install from unknown sources became app-specific, meaning users had to grant permission to each individual app (like a file manager or web browser) that they wanted to use to install APKs. This was a step towards better user control, but it still relied on the user actively managing these permissions.

The announcement of the upcoming developer verification rules, slated for September 2026, marked a more significant shift. This policy aims to mandate that all applications targeting newer Android versions must be signed by a verified developer. This has been interpreted by some as a move that could effectively curtail sideloading, especially for applications from developers who do not meet Google’s verification criteria.
However, Google’s subsequent clarification, introducing the "advanced flow," demonstrates a commitment to maintaining sideloading capabilities. This new system is a direct response to the concerns raised by the developer verification mandate, ensuring that users who still wish to sideload apps have a pathway to do so, albeit a more controlled one. This phased approach, with the initial focus on select regions and a broader rollout later, allows Google to monitor the effectiveness of the new measures and make necessary adjustments.
Supporting Data and Broader Context
The concern surrounding sideloading is rooted in the persistent threat of mobile malware. According to various cybersecurity reports, a significant percentage of mobile malware infections originate from unofficial app sources. For instance, statistics from cybersecurity firms often indicate that a substantial portion of detected Android malware is distributed through third-party app stores or direct APK downloads rather than through the Google Play Store. While Google’s Play Protect system actively scans for malicious apps, even within the Play Store, and has a robust detection rate, the open nature of sideloading presents a larger attack surface.

The introduction of verified developer requirements and the advanced flow directly addresses this vulnerability. By increasing the friction and the level of user intent required for sideloading, Google aims to reduce the number of successful malware installations. This is crucial for maintaining user trust and protecting the vast majority of Android users who rely on the Play Store for their app needs.
Furthermore, the move aligns with a global trend towards increased regulatory scrutiny of app distribution platforms. Governments worldwide are examining the role of major app stores in app security, data privacy, and fair competition. Google’s proactive measures, while driven by internal security concerns, also serve to demonstrate its commitment to a more secure and regulated digital environment, potentially preempting or influencing future regulatory actions.
Implications for Users and Developers
For the average Android user who exclusively uses the Google Play Store, these changes will likely have minimal to no impact. Their app installation habits will remain unaffected, and they will continue to benefit from the curated and scanned environment of the Play Store.

However, for a segment of Android users who are more tech-savvy, engage with third-party app stores, or frequently install independent or niche applications, the "advanced flow" will introduce an additional step in their process. This might lead to a slight inconvenience, but it is a trade-off for enhanced security. The requirement for a more deliberate action is intended to foster greater user awareness and responsibility when installing applications from unverified sources.
For developers, particularly those operating outside the mainstream app store model, the changes necessitate an understanding of the new verification processes. Developers who wish for their applications to be easily installable on modern Android devices will need to ensure they comply with Google’s developer verification standards. The existence of the advanced flow, however, provides a continued avenue for distribution, ensuring that innovation and alternative app development are not stifled entirely. It encourages a more transparent and accountable approach to app development and distribution, which can ultimately benefit the entire Android ecosystem.
In conclusion, Google’s updated approach to sideloading signifies a strategic move towards enhancing Android’s security posture without completely abandoning its open-source ethos. The "advanced flow" represents a more secure, albeit more complex, method for users to install applications from outside the Play Store, reflecting Google’s ongoing commitment to protecting its users while acknowledging the value of flexibility within the Android ecosystem. The long-term impact will likely be a reduction in malware distribution and a more secure environment for all Android users.